Blog
Check out the latest Technology and Computer News from the Team at iFix Computers.

Microsoft Edge Password Security Issue
May 2026
A recently discussed security concern involving Microsoft Edge and browser-stored passwords. You do not urgently need to abandon Edge But for business/admin users, there are now good reasons to re...

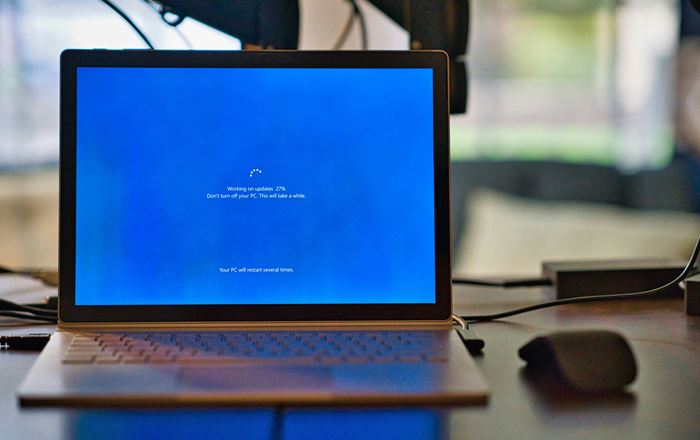
Windows 10 Support Has Ended — What You Need To Do Now
Dec 2025
After nearly a decade, Windows 10 has officially reached the end of support. That means Microsoft is no longer releasing security updates or patches for the operating system — and from a security and ...

How to Secure Your Home Wi-Fi: Simple Steps to Keep Others Out
Nov 2025
Your home Wi-Fi is the digital doorway to your personal and business life — and just like your front door, it needs a strong lock. While most people rely only on a password, there are several extra la...
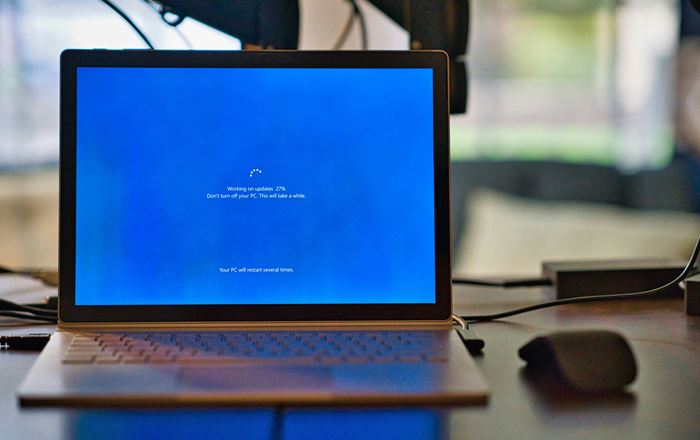
How to enable Microsoft ESU for Windows 10
Oct 2025
Microsoft has rolled out ESU - Extended Security Updates. To enable this you will need to do the following: Ensure that your Windows 10 device is updated to Version 22H2 (or required servicing baseli...

Risks of Side Loading Apps
Sep 2025
Why You Should Avoid Downloading Android Apps Outside of the Google Play Store In today’s digital world, apps are at the center of how we use our smartphones—whether for social media, banking, shoppin...

Windows 10 Life Line
Aug 2025
Microsoft Offers a Lifeline for Windows 10 Users—But It's Only Temporary With Windows 10 officially reaching its end of life on October 14, 2025, Microsoft has extended a short-term lifeline to perso...

Tech Support Scam
Jul 2025
Sure thing, Devon! Here's a blog post you can use for iFix Computers to help educate your customers: What Is a Tech Support Scam? Don’t Get Caught Out At iFix Computers, we’ve seen too many good peo...

Is Linux a Replacement for Windows
Jun 2025
Windows 11’s hardware requirements left many older PCs behind, pushing users to look for alternatives. One popular choice? Linux. But is it the right move for you? Let’s break it down. Pros of Using ...

Windows 10 EOL - What can you do?
Sep 2024
Windows 10's End of Life (EOL) in October 2025 means Microsoft will stop releasing updates, including security patches, and providing technical support for the operating system. For home users, this c...

Understanding RAM: What It Does and How Much You Need in Today's Workloads
Aug 2024
Random Access Memory (RAM) is a crucial component of any computer system. It serves as the short-term memory where the system stores data that is actively being used or processed. This allows for quic...

The Truth About Motherboards, Mainboards, and Logic Boards: What's in a Name?
Jul 2024
If you've ever delved into the world of computers, especially notebooks, you've likely encountered terms like "motherboard," "mainboard," and "logic board." Despite the different names, these terms al...

The Pros and Cons of Investing in Bitcoin and Other Cryptocurrencies
Jul 2024
Cryptocurrencies, led by Bitcoin, have captivated the attention of investors worldwide. Lauded for their potential to revolutionize the financial system, these digital assets offer both opportunities ...

The Urgency of Software Updates: Safeguarding Your Digital World
Jul 2024
In today's interconnected world, our reliance on technology is undeniable. From personal laptops to enterprise servers, software plays a crucial role in our daily activities. However, with great relia...

Enhancing Security for Work-from-Home Users: Best Practices and Essential Tools
Jun 2024
The shift to remote work has brought convenience and flexibility, but it has also introduced new cybersecurity challenges. For businesses and remote workers, ensuring robust security measures is param...

Understanding Man-in-the-Middle Attacks: Why Free Wi-Fi Isn't Safe and the Role of VPNs
Jun 2024
In our increasingly connected world, public Wi-Fi hotspots are a convenient way to access the internet on the go. Whether you're in a café, airport, or shopping mall, free Wi-Fi can be a lifesaver. Ho...

How to Install Chromium OS on an Unsupported Notebook or PC After Windows 10 Support Ends in October 2025
Jun 2024
As Windows 10 support comes to an end in October 2025, many older notebooks and PCs will no longer receive security updates or support from Microsoft. This doesn't mean these devices need to be retire...

The Critical Importance of Email Security
May 2024
In today's digital age, email remains a primary communication tool for both personal and professional use. Despite the rise of instant messaging and social media, email's versatility and formal tone m...

Setting up a new Online Business Pressence
May 2024
Starting Your Business with a Basic IT Setup: A Step-by-Step Guide When starting a new business, having a solid IT setup is crucial for ensuring smooth operations and establishing a professional onlin...

Choosing the Right Storage Solution for Your Business: Cloud vs. NAS
May 2024
In today's data-driven business landscape, the need for substantial storage solutions is undeniable. As companies amass vast amounts of data, deciding between cloud storage and local storage options l...
Up Coming Windows 11 on ARM
Apr 2024
ARM-based laptops, also known as ARM laptops, are a new breed of portable computing devices that utilize ARM (Advanced RISC Machine) architecture instead of the traditional x86 architecture found in m...

How to Check if you Can Run Windows 11
Apr 2024
The requirements for Windows 11 are: A compatible 64-bit processor - 8th Gen Intel and above, or Ryzen 3000 and above RAM: at least 4GB Storage: at least 64GB of available storage Security: TPM versi...

iFix Computers and Apple Computers
Apr 2024
We are thrilled to announce that iFix Computers has achieved a significant milestone in our journey – we are now an independent Apple Repair Agent. This exciting development marks a new chapter in our...

Protect Your Devices: The Benefits of Surge Protectors
Mar 2024
In today's digital age, our reliance on electronic devices is more prevalent than ever. From computers to notebooks, smartphones to gaming consoles, our homes and offices are filled with valuable elec...

Safeguarding Your Business: Windows 7 and Beyond
Mar 2024
In the ever-evolving landscape of technology, businesses often find themselves grappling with the challenge of maintaining legacy systems while embracing the advancements of the modern era. For th...

Protecting Your Data: A Tale of SSD Failure and Cloud Backup Triumph
Mar 2024
In the world of technology, unexpected setbacks can occur at any moment, putting your valuable data at risk. This week, we encountered a situation that underscores the importance of having a robust ba...

When is Help not Help?
Mar 2024
In the vast landscape of the internet, search engines serve as our trusted guides, helping us navigate through a sea of information with ease. However, lurking amidst the legitimate search results are...

Navigating the Future: Understanding Remote Managed IT Services
Feb 2024
In an era where digital transformation is the norm and remote work is becoming increasingly prevalent, businesses of all sizes are recognizing the importance of reliable and efficient IT support. Howe...
Windows 11 Requirements
Feb 2024
Whilst there are a number of requirements for Windows 11, the main two that may prevent you from being able to upgrade your Windows 10 to Windows 11 are: TPM 2.0 CPU Compatibility Trusted Platform M...

Sim Swap Scams
Feb 2024
In an increasingly digitized world, where our smartphones serve as gateways to our personal and financial information, it's more important than ever to remain vigilant against cyber threats. One such ...

The Need for Speed
Jan 2024
Unleashing the Need for Speed: HDD vs. SSD vs. NVMe In the realm of data storage, the speed at which information is retrieved can make a world of difference in your computing experience. Let's embark ...

Why We Recommend ESET
Jan 2024
Securing Your Digital Realm: The ESET Antivirus Advantage In the ever-expanding landscape of cybersecurity, choosing the right antivirus solution is paramount. ESET, a stalwart in the industry, stands...
Are LLM (Large Language Models) Actually AI?
Jan 2024
Decoding the Nuances: Large Language Models and the Quest for General AI In the grand tapestry of artificial intelligence (AI), there's an ongoing dialogue about the nature of large language models li...
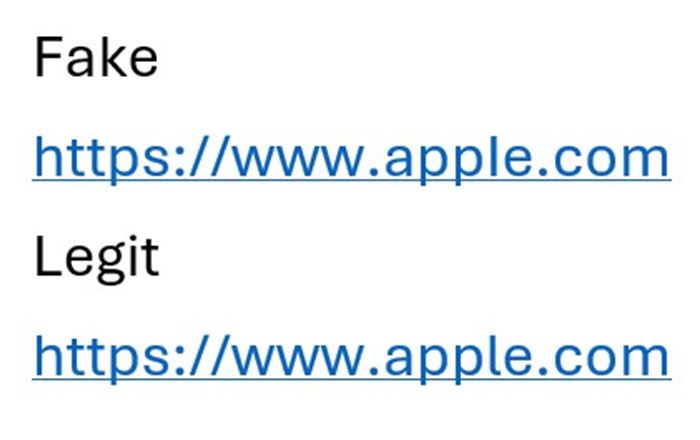
Can You Spot the Difference?
Jan 2024
What is a Homograph Attack? A homograph attack involves the use of characters that visually resemble legitimate characters but belong to different Unicode blocks. These characters can include letters,...

Beware of Pop-Up Scams: Protecting Yourself Online
Nov 2023
In the vast landscape of the internet, there exist both marvels and pitfalls. Unfortunately, one of the darker aspects is the prevalence of scams designed to exploit unsuspecting users. Among these, p...

MFA: Strengthening Security in a Digital World
Nov 2023
MFA, or Multi-Factor Authentication, is a critical security measure designed to enhance the protection of digital accounts and sensitive information. It goes beyond the traditional username and passwo...

The 3-2-1 Backup Rule: A Foundation for Data Protection
Nov 2023
The 3-2-1 backup rule is a fundamental principle in data protection and disaster recovery planning. It provides a clear and reliable framework for safeguarding critical information against...

End of Life Windows 10
Oct 2023
Understanding End of Life (EOL) in Technology In the ever-evolving landscape of technology, the term "End of Life" (EOL) carries significant weight. It refers to the stage in a product's lifecycle whe...

Speed up Your PC or Notebook
Oct 2023
Unlocking Performance: Why Upgrading to an SSD is the Best Bang for Your Buck In the fast-paced world of technology, staying ahead of the curve is crucial for optimal performance. One of the most impa...

Managed IT Support
Oct 2023
Elevating Your Tech Experience: iFix Computers as Your Managed IT Support Provider In today's fast-paced digital landscape, having reliable and efficient technology is paramount for personal and pro...

Security spotlight - Email Scams
Mar 2022
Are you email savvy? Despite being around since 1971, email is still a communication tool most of us use today. Its wide use and reliability continue to give it the edge against emerging messaging pla...

Should you upgrade to Windows 11?
Dec 2021
On the 5th October 2021, Microsoft quietly started rolling out Windows 11 in New Zealand - 6 years and 4 months after the release of Windows 10. You might have seen the notifications appear on your co...

Security spotlight - Remote Access Scams
Sep 2021
As New Zealand shifts around alert levels and gets used to the idea of various forms of lock-down, one thing's for sure - we are spending a lot more time in front of our computers and internet-enabled...